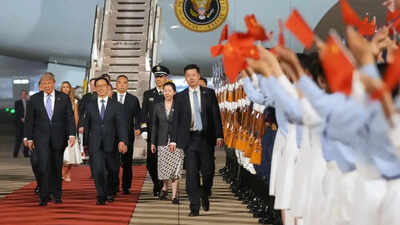
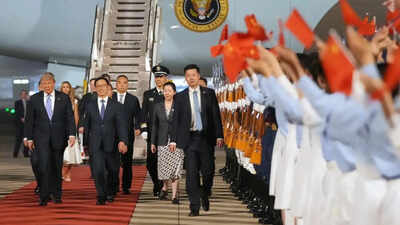
US President Donald Trump’s team’s arrival in Beijing was marked amid a digital lockdown. Accompanied by some of America’s most influential business and technology leaders, even as US officials travelling with the delegation operated under strict cybersecurity precautions.Among the executives joining Trump on the trip were Nvidia chief Jensen Huang, Apple chief Tim Cook, Tesla and SpaceX owner Elon Musk, BlackRock chief Larry Fink, as well as senior figures from Meta, Visa, JP Morgan, Boeing and Cargill. More than a dozen American corporate leaders were part of the delegation amid ongoing US-China negotiations over trade, technology and investment.According to a Fox News Digital report, many US officials travelling to China left behind their personal phones and laptops, instead carrying temporary “clean” devices and tightly controlled communication systems to reduce the risk of hacking, surveillance or data collection.As per the report, China operate under the assumption that “anything brought into China — phones, laptops, tablets or even hotel Wi-Fi connections — should be treated as potentially compromised”.
Restrictions and precautions followed by US officials in China
- Personal phones and laptops are often left behind before entering China.
- Officials are issued temporary “clean” or “burner” devices with limited data.
- Access to cloud storage, synced apps and personal accounts is heavily restricted.
- Officials avoid connecting to hotel Wi-Fi or public charging stations.
- Only government-approved chargers, battery packs and accessories are used.
- Communication is routed through tightly controlled channels or temporary accounts.
- Some sensitive discussions are relayed in person instead of digitally.
- Devices may be checked before and after the trip for signs of tampering.
Even routine communication becomes difficult under such restrictions, making officials rely on temporary accounts, controlled communication channels and, in some cases, in-person relays instead of encrypted apps or synchronised cloud systems. No form of electronic communication is considered “safe” in China, and digital activities are limited to only what is crucial to the purpose of the visit.
Burner phones, secure zones and SCIFs
Officials and executives may be issued temporary devices carrying known “golden images”. This is so security teams can later determine comparing the before and after use to determine whether they have been tampered with.
What are ‘golden image’ devices?
- These are pre-configured phones or laptops prepared by security teams before travel.
- Officials use them only for the duration of the visit.
- After the trip, cybersecurity teams compare the devices against the original “golden image” setup to detect possible hacking or surveillance attempts.
The report also said US officials travelling overseas often rely on temporary sensitive compartmented information facilities, or SCIFs, which are secure spaces designed to prevent electronic surveillance and eavesdropping.
US cites years of alleged Chinese cyber espionage
US intelligence agencies have for years accused Beijing-linked groups of targeting American government systems, telecommunications networks, defence contractors and critical infrastructure. Washington has repeatedly cited alleged Chinese cyber campaigns including Volt Typhoon and Salt Typhoon as examples of state-backed espionage operations.The issue gained wider public attention in 2023 after a suspected Chinese surveillance balloon crossed the continental United States before being shot down by the US military. American officials later described it as part of a broader surveillance effort linked to Beijing.
China rejects surveillance allegations
China has consistently denied allegations of unlawful surveillance or cyber espionage.“In China, personal privacy is protected by law,” Fox News Digital reported citing Chinese Embassy spokesperson Liu Pengyu. “The Chinese government places a high priority on protecting data privacy and security in accordance with the law. It has never required and will never require enterprises or individuals to collect or store data in violation of the law.”
China’s digital monitori
China maintains an extensive state-led digital governance framework under laws and regulations introduced in recent years. The country’s Cybersecurity Law, Data Security Law and Personal Information Protection Law regulate how data is collected, stored and transferred within China.Chinese authorities also operate broad internet controls under what Beijing describes as its cyber sovereignty model, which includes monitoring online content and restricting access to several foreign digital platforms.Official Chinese government documents state that these measures are aimed at protecting national security, maintaining social stability and safeguarding personal information. Beijing has also defended the use of surveillance technologies, including facial recognition systems and internet monitoring tools, as necessary for public safety and crime prevention.The high-profile visit comes as Washington and Beijing attempt to stabilise economic ties despite continuing tensions over technology, trade, cybersecurity and national security.